Music
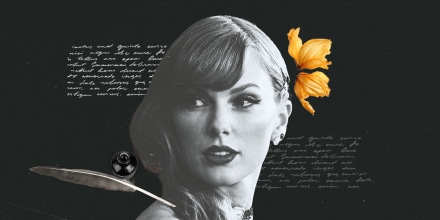
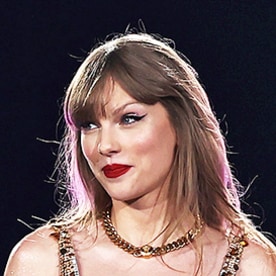
Taylor Swift’s ‘Tortured Poets Department’ live updates: What fans are saying
Taylor Swift’s 11th studio album is a collection of 31 songs, including tracks from her “Anthology” double album. Revisit everything we covered on her Easter eggs, lyrics and more.
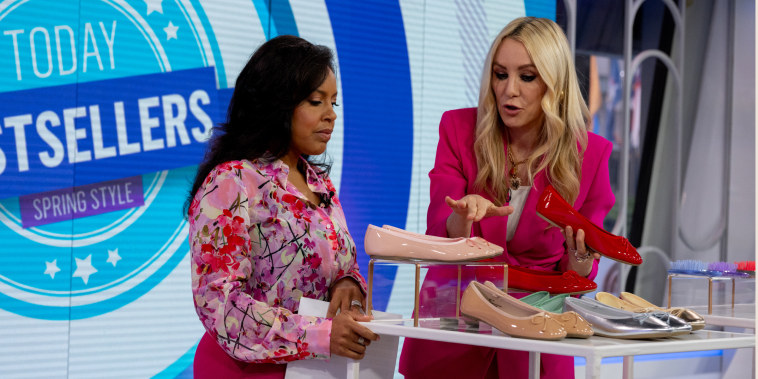
On the Show
Saw it on TODAY? Find recipes, resources, videos and more.
Saw it on TODAY
The Tortured Poets Department
The chairman of the Tortured Poets Department dropped her long-awaited 11th album on April 19
More from Shop TODAY
Our Most Saved Recipes
These are the recipes you're saving the most thanks to our new accounts experience!
Health & Wellness
Get health tips, read personal essays, weight-loss stories.
Food
The latest food trends, easy recipes and healthy meal ideas to help you cook smarter.
Food trends
Recipes from TODAY
Parents
Stories, trends and tips for every stage of parenthood... because we're all in this together
Life
Get the best inspiration, quotes, and holiday ideas from TODAY editors.
Astrology
Find your monthly horoscopes, astrological profiles of zodiac signs, and info about other spiritual practices.
Pop Culture
Get entertainment and celebrity news and trending stories.
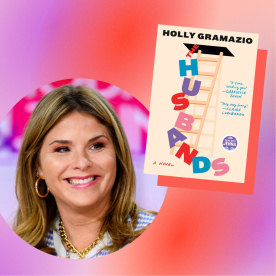
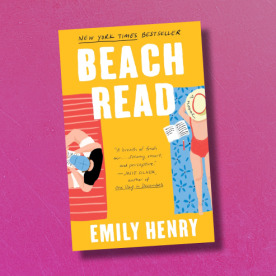
Books
Get TODAY's list of the best books to read, recommendations, excerpts and more
Read With Jenna
What to read next
Relationships
Find inspiring stories and expert advice on how to have a healthy relationship with yourself and others.